It’s certainly an issue no business, much less one involved in trucking or logistics, really wants to think about: the threat posed by “company insiders” to information technology (IT) systems.
Whether conducted by someone who hires on with ill-intent already programmed from the start, or a disgruntled employee looking to extract some malicious payback on the way out the door, the “insider threat” to trucking IT can’t be taken lightly.
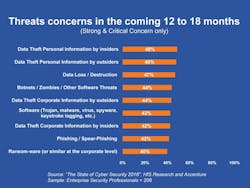
Indeed a recent survey The State of Cybersecurity and Digital Trust 2016 conducted by HfS Research on behalf of global consulting firm Accenture with some 208 C-level security executives and other IT professionals found that “insider threats” were far and away their top IT security concern.
In fact a majority of those polled in this survey (69%) said they experienced an attempted or successful theft or corruption of data by insiders during the prior 12 months.This “insider risk” will continue to be an issue, added Kelly Bissell, a senior managing director at Accenture Security, with security professionals’ concerns over insider theft of corporate information alone rising by nearly two-thirds for the coming 12 to 18 month period (see chart at right).
“Our research paints a sobering picture. Security leaders believe threats are not going away; in fact they expect them to increase and hinder their ability to safeguard critical data and establish digital trust,” Bissell added.
“At the same time, while organizations want to invest in advanced cyber technologies, they simply don’t have enough budget to recruit or train skilled people to use that technology effectively,” Bissell noted.
Indeed, despite having access to so-called “advanced technology solutions” for data protection, nearly half of all respondents (48%) indicate they are either strongly or critically concerned about insider data theft and malware infections (42%) in the next 12 to 18 months.
When asked about current funding and staffing levels, some 42% of respondents to Accenture’s survey said they need more budget for hiring cybersecurity professionals and for training.On top of that, more than half (54%) of those polled also indicated that their current employees are under-prepared to prevent security breaches and the numbers are only slightly better when it comes to detecting (47%) and responding (45%) to incidents.
Greg Byles, CEO at Global Technology Resources, Inc. (GTRI) added more sobering thoughts to this trend, noting that according to the 2013 US State of Cybercrime Survey, over 50% of participating organizations experienced an insider incident and 53% of affected organizations stated that the damage was greater than the loss by outsider attacks – scary data for motor carrier executives to consider, especially as trucking and logistics become more and more digitized every day.
“Surprisingly insider cyber-attacks are under-reported compared to outsider attacks and only a few cases ever make it into the public eye giving organizations the false belief that these attacks are rarer than their outsider counterparts,” noted Byles in a statement. “While we understand that technology alone will not eradicate the problem of insider cyber-attacks, the right technology is a critical component of fighting these attacks.”
Yet another source, the Insider Threat Spotlight Report, a survey of over 500 IT security professionals co-sponsored by security firm Veriato, also noted that nearly half of those it polled witnessed an increase in insider attacks over the last 12 months.
The biggest “insider threats,” they say, come from managers with access to sensitive information, with 67% believing that the fact insiders have credentialed access makes insider attacks more difficult to prevent.
“If you are not looking for insider attacks, you are simply not seeing them,” noted Mike Tierney, CEO at Veriato, in a statement.
“Your organization is, and will be, compromised by insiders, and to prevent attacks, you need to have some controls in place that are specifically focused on the insider,” he added. “Trust is a strategy for failure.”
[Whoa; is THAT harsh advice for today’s business culture or what?!]
Here are a few more data points from this particular poll for trucking executives in charge of IT systems to chew on:
- More than half of the organizations in the poll (58%) said they still lack the appropriate controls to prevent insider attacks with just under half (44%) unaware if their firm actually experienced an insider attack at all.
- An IT system’s “endpoint” is the most common launching point for an insider attack, the survey found, by a wide margin; in fact 58% more than the next most common launching point, which is mobile devices. Tracking file movement across the network is a critical component of a data security strategy, according to 75% of respondents, with 57% pointing to databases as the most vulnerable asset to an outside attack.
- The three barriers most cited by those polled as keys to better insider threat management include lack of training and expertise (60%), insufficient budgets (50%) and lack of collaboration between departments (48%).
- Notably, lack of collaboration is the barrier with the highest gain since the previous survey, moving up 10 percentage points.
“Not only do companies need to do a better job of educating employees about what data they are able to share or take with them when they leave, but the departments within the companies need to do a better job working together to share any red flags they are seeing, such as from disgruntled employees,” Tierney added.
“Such collaboration, coupled with user behavior monitoring and analytics solutions, can play a huge role in detecting and preventing insider attacks that could potentially cost hundreds of thousands,” he stressed.
Something for motor carriers to keep in mind as the digitization of trucking only continues to gain speed.